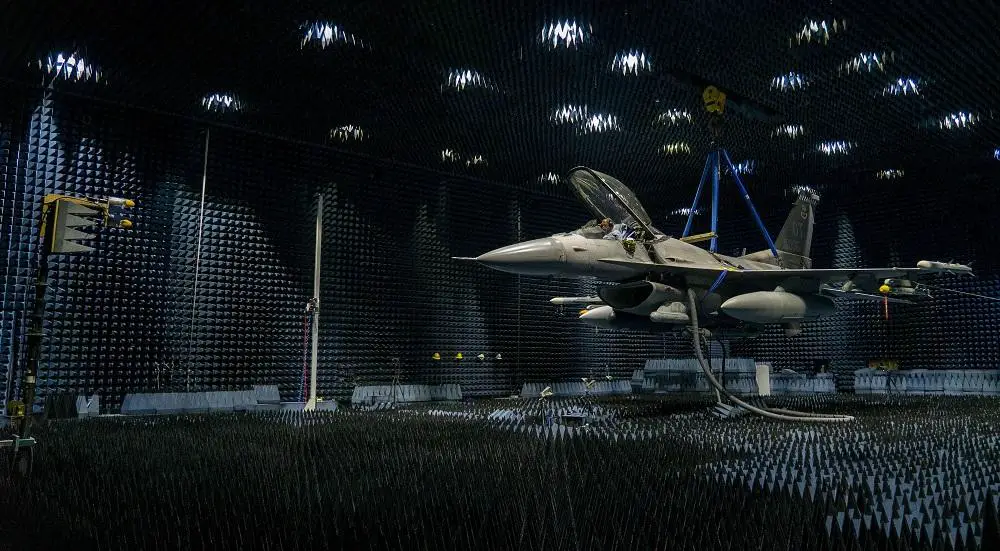
The operational assessment of the Angry Kitten Combat Pod electronic attack system in April demonstrated rapid reprogramming between flights. This combat pod, an updated version of the Georgia Tech Research Institute Angry Kitten pod, simulates enemy electronic attack signals during Air Force test and training missions. The Air Force Research Laboratory’s Strategic Development Planning and Experimentation Office funded this operational assessment as part of the App-Enabled Rapidly Reprogrammable Electronic warfare/electromagnetic Systems experiment campaign, or AERRES. Given the success of the pod in training and demonstrated ability to be reprogrammed, Air Combat Command recommended four pods be converted into combat pods to provide attack capabilities against enemy radio frequency threat systems, instead of simulating them.
Keith Kirk, the experiment program manager said,”AERRES is assessing the operational utility and competitive advantages of open hardware/software architectures and standards to provide app-enabled electronic warfare/electromagnetic systems solutions. He said Air Force leaders noticed the test because they expect to employ more open architecture software to allow agile changes in future systems. Over the past four years, it has been well documented in the strategic guidance that we have to do this. This is the first operational assessment of a potentially deployable and combat-ready electronic warfare system for fighter aircraft moving in that direction.”
The experiment aimed to show how this new government-owned architecture could be used to better counter threat systems that use software-defined radars to quickly change their radio frequency signature to make it more difficult for U.S. aircraft to identify and attack them. Historically, Air Force electronic warfare systems were designed to have tightly coupled software and hardware, which were effective, but also took considerable time and funding to update. The Angry Kitten architecture provides greater flexibility to update or reprogram the system as the electronic warfare environment changes. Similar to a smartphone and digital app store, electronic warfare/electromagnetic systems need to be quickly updated or loaded with new software to defeat complex emitters and constantly changing electromagnetic systems threats.
The data files use an open-source programming language, which enables programmers to design effective jamming techniques against threats with known radio frequency signature data. Graham said the techniques were evaluated over many months to improve accuracy and efficiency. Multiple organizations, including the 36th Electronic Warfare Squadron, Georgia Tech Research Institute, Air National Guard-Air Force Reserve Test Center and the U.S. Air Force Air Warfare Center, worked to ensure the most current techniques were programmed. Before the flight test event, programmers developed the specific mission data files for the system, and the team worked with the Air Force Life Cycle Management Center’s Agile Combat Support Directorate to verify and validate these updates in labs at Robins Air Force Base, Georgia. Team members created next-day data file updates at Nellis Air Force Base, Nevada, during the operational assessment.